You signed in with another tab or window. Reload to refresh your session.You signed out in another tab or window. Reload to refresh your session.You switched accounts on another tab or window. Reload to refresh your session.Dismiss alert
Copy file name to clipboardExpand all lines: views/md/introduction.md
+23-23Lines changed: 23 additions & 23 deletions
Original file line number
Diff line number
Diff line change
@@ -1,20 +1,20 @@
1
1
## What is JSON Web Token?
2
-
JSON Web Token (JWT) is an open standard ([RFC 7519](https://tools.ietf.org/html/rfc7519)) that defines a compact and self-contained way for securely transmitting information between parties as a JSON object. This information can be verified and trusted because it is digitally signed. JWTs can be signed using a secret (with **HMAC** algorithm) or a public/private key pair using **RSA**.
2
+
JSON Web Token (JWT) is an open standard ([RFC 7519](https://tools.ietf.org/html/rfc7519)) that defines a compact and self-contained way for securely transmitting information between parties as a JSON object. This information can be verified and trusted because it is digitally signed. JWTs can be signed using a secret (with the **HMAC** algorithm) or a public/private key pair using **RSA**.
3
3
4
4
Let's explain some concepts of this definition further.
5
5
6
-
-**Compact**: Because of its size, it can be sent through an URL, POST parameter, or inside an HTTP header. Additionally, due to its size its transmission is fast.
6
+
-**Compact**: Because of its smaller size, JWTs can be sent through an URL, POST parameter, or inside an HTTP header. Additionally, the smaller size means transmission is fast.
7
7
8
-
-**Self-contained**: The payload contains all the required information about the user, to avoid querying the database more than once.
8
+
-**Self-contained**: The payload contains all the required information about the user, avoiding the need to query the database more than once.
9
9
10
10
## When should you use JSON Web Tokens?
11
-
There are some scenarios where JSON Web Tokens are useful:
11
+
Here are some scenarios where JSON Web Tokens are useful:
12
12
13
-
-**Authentication**: This is the typical scenario for using JWT, once the user is logged in, each subsequent request will include the JWT, allowing the user to access routes, services, and resources that are permitted with that token. Single Sign On is a feature that widely uses JWT nowadays, because of its small overhead and its ability to be easily used among systems of different domains.
13
+
-**Authentication**: This is the most common scenario for using JWT. Once the user is logged in, each subsequent request will include the JWT, allowing the user to access routes, services, and resources that are permitted with that token. Single Sign On is a feature that widely uses JWT nowadays, because of its small overhead and its ability to be easily used across different domains.
14
14
15
-
-**Information Exchange**: JSON Web Tokens are a good way of securely transmitting information between parties, because as they can be signed, for example using public/private key pairs, you can be sure that the senders are who they say they are. Additionally, as the signature is calculated using the header and the payload, you can also verify that the content hasn't changed.
15
+
-**Information Exchange**: JSON Web Tokens are a good way of securely transmitting information between parties, because as they can be signed, for example using public/private key pairs, you can be sure that the senders are who they say they are. Additionally, as the signature is calculated using the header and the payload, you can also verify that the content hasn't been tampered with.
16
16
17
-
## Which is the JSON Web Token structure?
17
+
## What is the JSON Web Token structure?
18
18
JSON Web Tokens consist of three parts separated by dots (`.`), which are:
19
19
20
20
- Header
@@ -29,7 +29,7 @@ Let's break down the different parts.
29
29
30
30
### Header
31
31
32
-
The header *typically* consists of two parts: the type of the token, which is JWT, and the hashing algorithm such as HMAC SHA256 or RSA.
32
+
The header *typically* consists of two parts: the type of the token, which is JWT, and the hashing algorithm being used, such as HMAC SHA256 or RSA.
33
33
34
34
For example:
35
35
@@ -47,7 +47,7 @@ Then, this JSON is **Base64Url** encoded to form the first part of the JWT.
47
47
The second part of the token is the payload, which contains the claims. Claims are statements about an entity (typically, the user) and additional metadata.
48
48
There are three types of claims: *reserved*, *public*, and *private* claims.
49
49
50
-
-**Reserved claims**: These are a set of predefined claims, which are not mandatory but recommended, thought to provide a set of useful, interoperable claims. Some of them are: **iss** (issuer), **exp** (expiration time), **sub** (subject), **aud** (audience), among others.
50
+
-**Reserved claims**: These is a set of predefined claims which are not mandatory but recommended, to provide a set of useful, interoperable claims. Some of them are: **iss** (issuer), **exp** (expiration time), **sub** (subject), **aud** (audience), and others.
51
51
52
52
> Notice that the claim names are only three characters long as JWT is meant to be compact.
53
53
@@ -70,7 +70,7 @@ The payload is then **Base64Url** encoded to form the second part of the JSON We
70
70
### Signature
71
71
To create the signature part you have to take the encoded header, the encoded payload, a secret, the algorithm specified in the header, and sign that.
72
72
73
-
For example if you want to use the HMAC SHA256 algorithm, the signature will be created in the following way.
73
+
For example if you want to use the HMAC SHA256 algorithm, the signature will be created in the following way:
74
74
75
75
```
76
76
HMACSHA256(
@@ -79,51 +79,51 @@ HMACSHA256(
79
79
secret)
80
80
```
81
81
82
-
The signature is used to verify that the sender of the JWT is who it says it is and to ensure that the message was't changed in the way.
82
+
The signature is used to verify that the sender of the JWT is who it says it is and to ensure that the message wasn't changed along the way.
83
83
84
84
### Putting all together
85
85
86
-
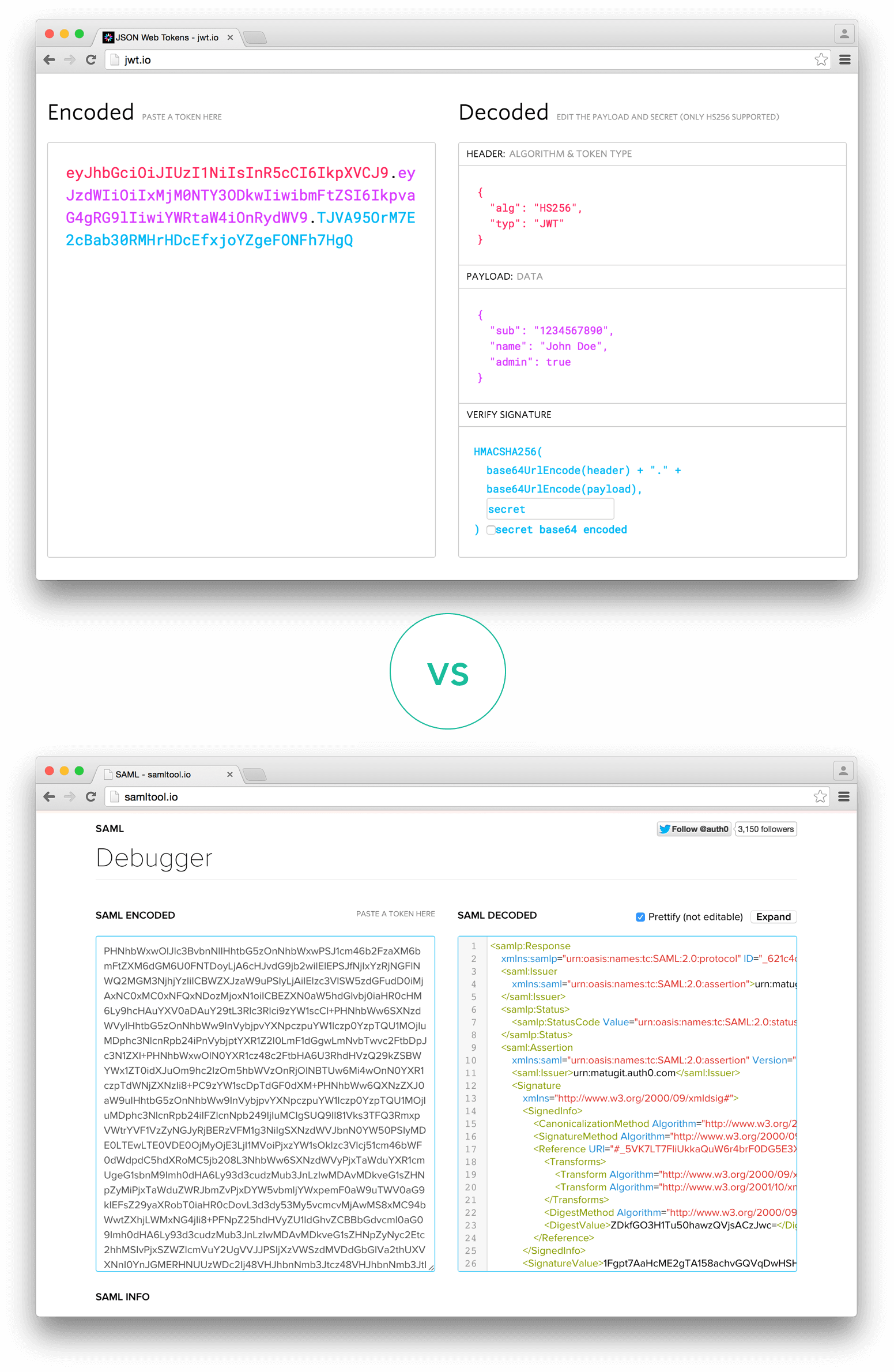
The output is three Base64 strings separated by dots that can be easily passed in HTML and HTTP environments, while being more compact compared to XML-based standards such as SAML.
86
+
The output is three Base64 strings separated by dots that can be easily passed in HTML and HTTP environments, while being more compact when compared to XML-based standards such as SAML.
87
87
88
88
The following shows a JWT that has the previous header and payload encoded, and it is signed with a secret.
In authentication, when the user successfully logs in using his credentials, a JSON Web Token will be returned and must be saved locally (typically in local storage, but cookies can be also used), instead of the traditional approach of creating a session in the server and returning a cookie.
97
97
98
-
Whenever the user wants to access a protected route or resource, it should send the JWT, typically in the **Authorization** header using the **Bearer** schema. Therefore the content of the header should look like the following.
98
+
Whenever the user wants to access a protected route or resource, the user agent should send the JWT, typically in the **Authorization** header using the **Bearer** schema. The content of the header should look like the following:
99
99
100
100
```
101
101
Authorization: Bearer <token>
102
102
```
103
103
104
-
This is a stateless authentication mechanism as the user state is never saved in the server memory.
105
-
The server's protected routes will check for a valid JWT in the Authorization header, and if there is, the user will be allowed. As JWTs are self-contained, all the necessary information is there, reducing the need of going back and forward to the database.
104
+
This is a stateless authentication mechanism as the user state is never saved in server memory.
105
+
The server's protected routes will check for a valid JWT in the Authorization header, and if it's present, the user will be allowed to access protected resources. As JWTs are self-contained, all the necessary information is there, reducing the need to query the database multiple times.
106
106
107
-
This allows to fully rely on data APIs that are stateless and even make requests to downstream services. It doesn't matter which domains are serving your APIs, as Cross-Origin Resource Sharing (CORS) won't be an issue as it doesn't use cookies.
107
+
This allows you to fully rely on data APIs that are stateless and even make requests to downstream services. It doesn't matter which domains are serving your APIs, so Cross-Origin Resource Sharing (CORS) won't be an issue as it doesn't use cookies.
108
108
109
109
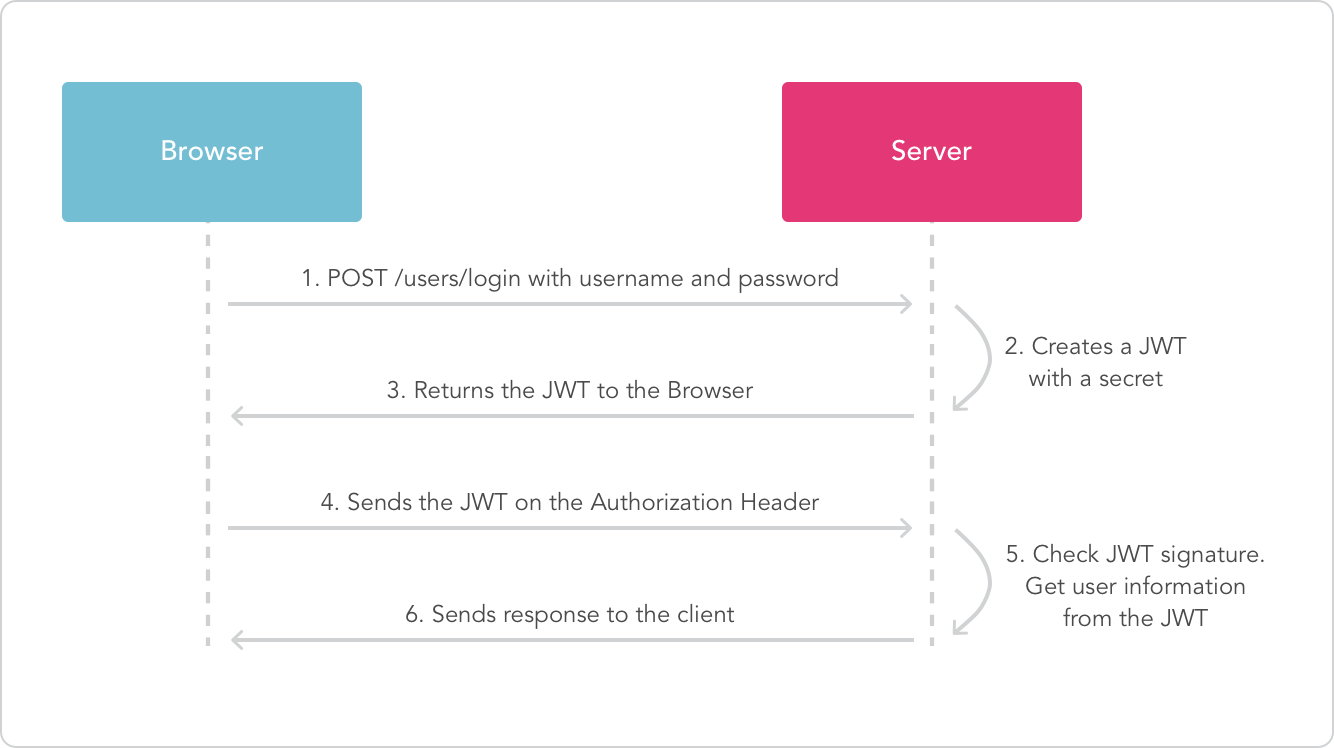
The following diagram shows this process:
110
110
111
111
112
112
113
113
## Why should we use JSON Web Tokens?
114
114
115
-
Let's talk about the benefits of **JSON Web Tokens (JWT)**comparing it to **Simple Web Tokens (SWT)** and **Security Assertion Markup Language Tokens (SAML)**.
115
+
Let's talk about the benefits of **JSON Web Tokens (JWT)**when compared to **Simple Web Tokens (SWT)** and **Security Assertion Markup Language Tokens (SAML)**.
116
116
117
-
As JSON is less verbose than XML, when it is encoded its size is also smaller; making JWT more compact than SAML. This makes JWT a good choice to be passed in HTML and HTTP environments.
117
+
As JSON is less verbose than XML, when it is encoded its size is also smaller, making JWT more compact than SAML. This makes JWT a good choice to be passed in HTML and HTTP environments.
118
118
119
-
Security-wise, SWT can only be symmetric signed by a shared secret using the HMAC algorithm. While JWT and SAML tokens can also use a public/private key pair in the form of a X.509 certificate to sign them. However, signing XML with XML Digital Signature without introducing obscure security holes is very difficult compared to the simplicity of signing JSON.
119
+
Security-wise, SWT can only be symmetricly signed by a shared secret using the HMAC algorithm. However, JWT and SAML tokens can use a public/private key pair in the form of a X.509 certificate for signing. Signing XML with XML Digital Signature without introducing obscure security holes is very difficult when compared to the simplicity of signing JSON.
120
120
121
-
JSON parsers are common in most programming languages, because they map directly to objects, conversely XML doesn't have a natural document-to-object mapping. This makes it easier to work with JWT than SAML assertions.
121
+
JSON parsers are common in most programming languages because they map directly to objects. Conversely, XML doesn't have a natural document-to-object mapping. This makes it easier to work with JWT than SAML assertions.
122
122
123
-
Regarding usage, JWT is used at an Internet scale. This highlights the ease of clientside processing of the JSON Web token on multiple platforms, especially, mobile.
123
+
Regarding usage, JWT is used at Internet scale. This highlights the ease of client-side processing of the JSON Web token on multiple platforms, especially mobile.
124
124
125
125
126
126
_Comparison of the length of an encoded JWT and an encoded SAML_
127
127
128
128
129
-
If you want to read more about JSON Web Tokens and even start using them to perform authentication in your own applications, browse to the [JSON Web Token landing page](http://auth0.com/learn/json-web-tokens)in Auth0.
129
+
If you want to read more about JSON Web Tokens and even start using them to perform authentication in your own applications, browse to the [JSON Web Token landing page](http://auth0.com/learn/json-web-tokens)at Auth0.
0 commit comments